Introduction
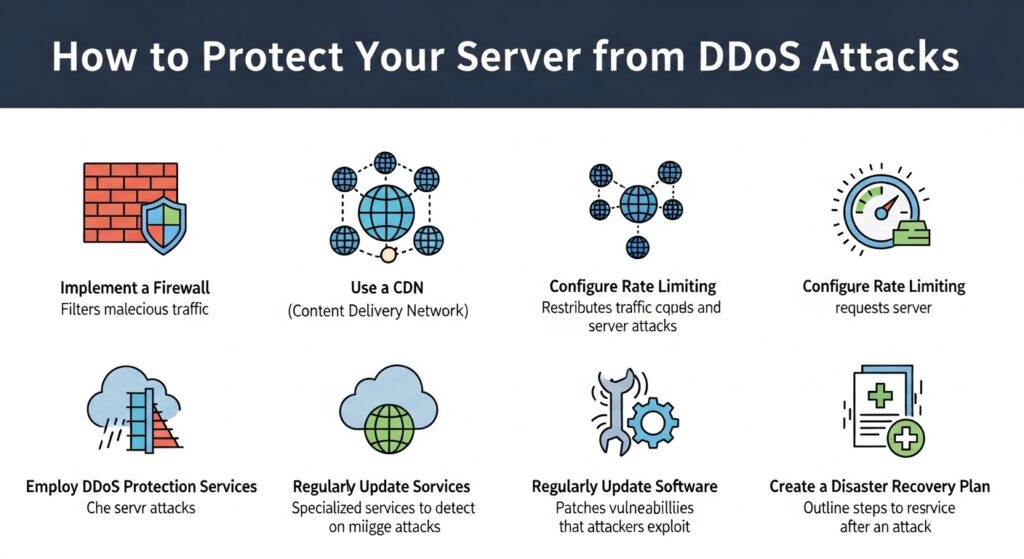
Distributed Denial of Service attacks are one of the most common threats faced by modern servers. A DDoS attack works by overwhelming your server with a massive amount of traffic, making your website or application unavailable to legitimate users. These attacks can come from thousands of compromised systems at once, making them difficult to stop without proper preparation. This guide explains how to protect your server from DDoS attacks using practical and effective strategies.
Understanding DDoS Attacks
Before implementing protection, it is important to understand how DDoS attacks work. Attackers use networks of infected machines known as botnets to send large volumes of requests to a target server. This can exhaust bandwidth, CPU, or memory resources, causing the server to slow down or crash completely.
There are different types of DDoS attacks. Some target network bandwidth, while others focus on application level vulnerabilities. A strong defense requires a combination of strategies to handle multiple attack types.
1. Use a Content Delivery Network
A Content Delivery Network helps distribute traffic across multiple servers located in different regions. Instead of all traffic hitting your origin server, it is spread across a global network. This reduces the impact of large traffic spikes and helps absorb malicious requests before they reach your server.
2. Implement Rate Limiting
Rate limiting controls how many requests a user can make within a specific time period. This helps prevent attackers from flooding your server with repeated requests. You can configure rate limiting at the web server level or through firewall rules.
3. Configure a Web Application Firewall
A Web Application Firewall filters incoming traffic and blocks suspicious patterns. It can detect and stop malicious requests such as repeated login attempts or unusual traffic spikes. A properly configured firewall acts as a strong barrier against many DDoS attempts.
4. Use Load Balancing
Load balancing distributes incoming traffic across multiple servers. If one server becomes overwhelmed, traffic is redirected to others. This not only improves performance but also increases resilience against attacks.
5. Enable Network Level Protection
Work with your hosting provider or network administrator to enable protection at the network level. Many providers offer built in DDoS mitigation services that detect and filter malicious traffic before it reaches your server.
6. Harden Your Server Configuration
Optimize your server settings to handle high traffic loads. Adjust connection limits, timeouts, and buffer sizes. Disable unnecessary services to free up resources. A well optimized server can handle more traffic without failing.
7. Monitor Traffic in Real Time
Continuous monitoring helps you detect unusual traffic patterns early. Use monitoring tools to track bandwidth usage, request rates, and system performance. Early detection allows you to respond quickly before the attack escalates.
8. Block Suspicious IP Addresses
Identify and block IP addresses that generate excessive or suspicious traffic. You can automate this process using security tools that analyze logs and apply blocking rules dynamically.
9. Prepare a Response Plan
Have a clear plan in place for responding to DDoS attacks. This should include steps for identifying the attack, activating mitigation tools, and communicating with your hosting provider. A quick and organized response can significantly reduce downtime.
10. Keep Software and Systems Updated
Regular updates ensure your server is protected against known vulnerabilities. Attackers often exploit outdated software to amplify DDoS attacks. Keeping everything updated strengthens your overall security posture.
SEO Keywords and Optimization
Primary keywords include DDoS protection, server security, prevent DDoS attacks, and network security. Secondary keywords include traffic filtering, rate limiting, load balancing, web application firewall, and server hardening.
To improve SEO, use structured headings, include keywords naturally, and provide detailed actionable information. High quality content that answers user queries effectively will rank better and attract more readers.
Conclusion
Protecting your server from DDoS attacks requires a layered approach. No single solution can stop every attack, but combining multiple strategies creates a strong defense. By using traffic filtering, monitoring tools, and scalable infrastructure, you can ensure your server remains stable and accessible even under heavy attack conditions.
Image Generation Prompt
A futuristic cybersecurity illustration showing a server under DDoS attack with massive incoming traffic streams being blocked by shields, firewalls, and distributed network nodes, glowing red attack lines versus blue defense systems, dark background, high detail, 4k resolution